In Brief:
- Essential Connectors: Blockchain bridges are vital for asset and data transfers across isolated blockchain networks, enhancing the functionality and scope of Web3.
- Security Risks Highlighted: Despite their importance, bridges pose significant security threats due to their complex structure and role in handling sizeable digital assets.
- Strengthening Defenses: Strategies for securing bridges include rigorous private key management, transaction monitoring, rate limits, and ongoing security audits.
Introduction to Blockchain Bridges
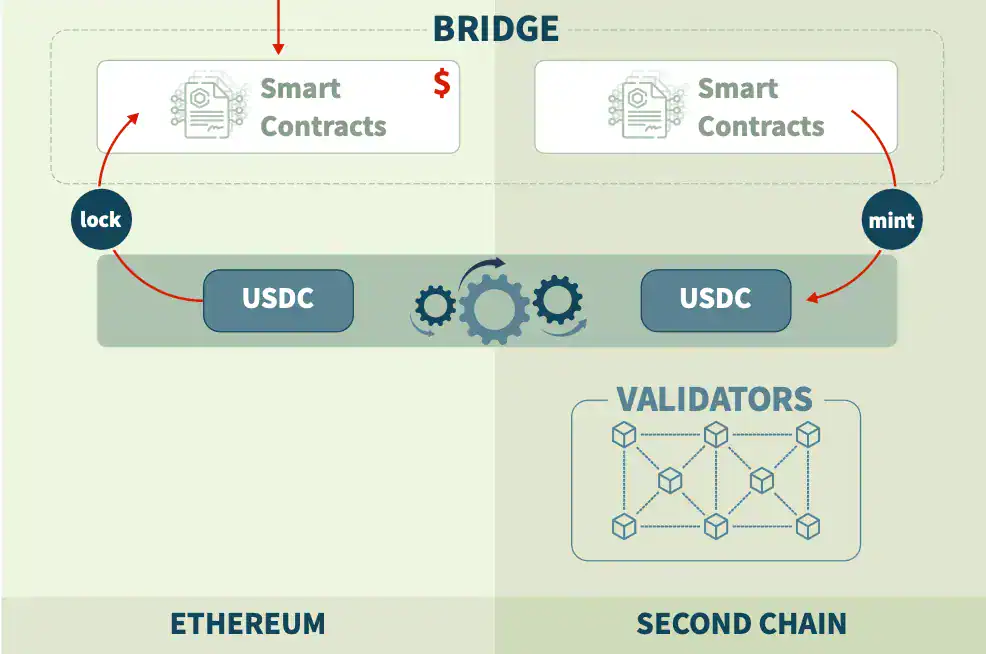
Blockchain bridges serve as critical infrastructure in the Web3 environment by enabling seamless communication and transaction execution between different blockchain networks. This interconnectivity allows distinct blockchains to transfer tokens, share data, and execute smart contracts, thus breaking down barriers and fostering a truly integrated digital asset ecosystem.
The Significance of Bridge Security
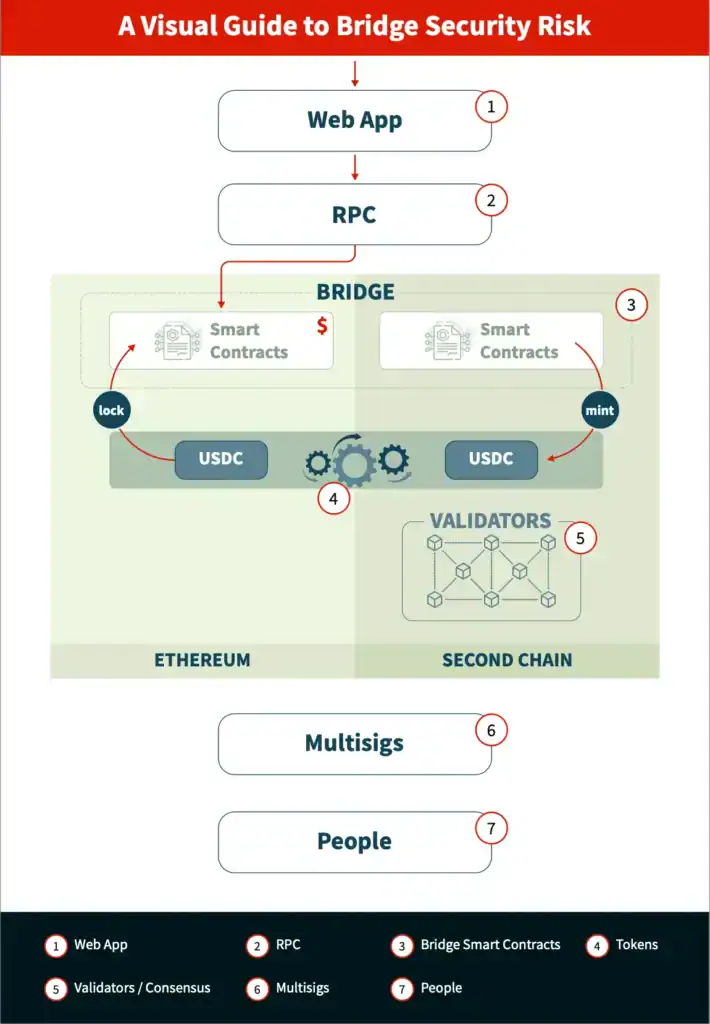
The fundamental role of blockchain bridges in managing transfers of considerable sums makes them a prime target for cyberattacks. The security of these platforms is a major concern, especially as billions of dollars worth of digital assets have already been compromised through bridge vulnerabilities. The intricate nature of these systems, which involves smart contracts, validator protocols, and multiple layers of communication, adds to the challenge of securing them adequately.
Recognizing Common Security Loopholes
Several vulnerabilities plague blockchain bridges:
- Compromised Key Management: Many bridges rely on validators whose keys, if stolen or misused, can allow unauthorized control over the bridge.
- Insufficient Monitoring: Without effective real-time surveillance, illicit activities can remain undetected, facilitating the theft of assets.
- Smart Contract Flaws: Errors in complex smart contracts used in operations like asset-locking or -minting can result in devastating losses.
- Lack of Safeguards: Absence of transaction limits can exacerbate the damage done by attacks, potentially allowing a swift drain of all bridge-held funds.
Best Practices for Enhanced Security
To better protect these vital components of the blockchain ecosystem, a multi-layered security approach is paramount. Effective practices include:
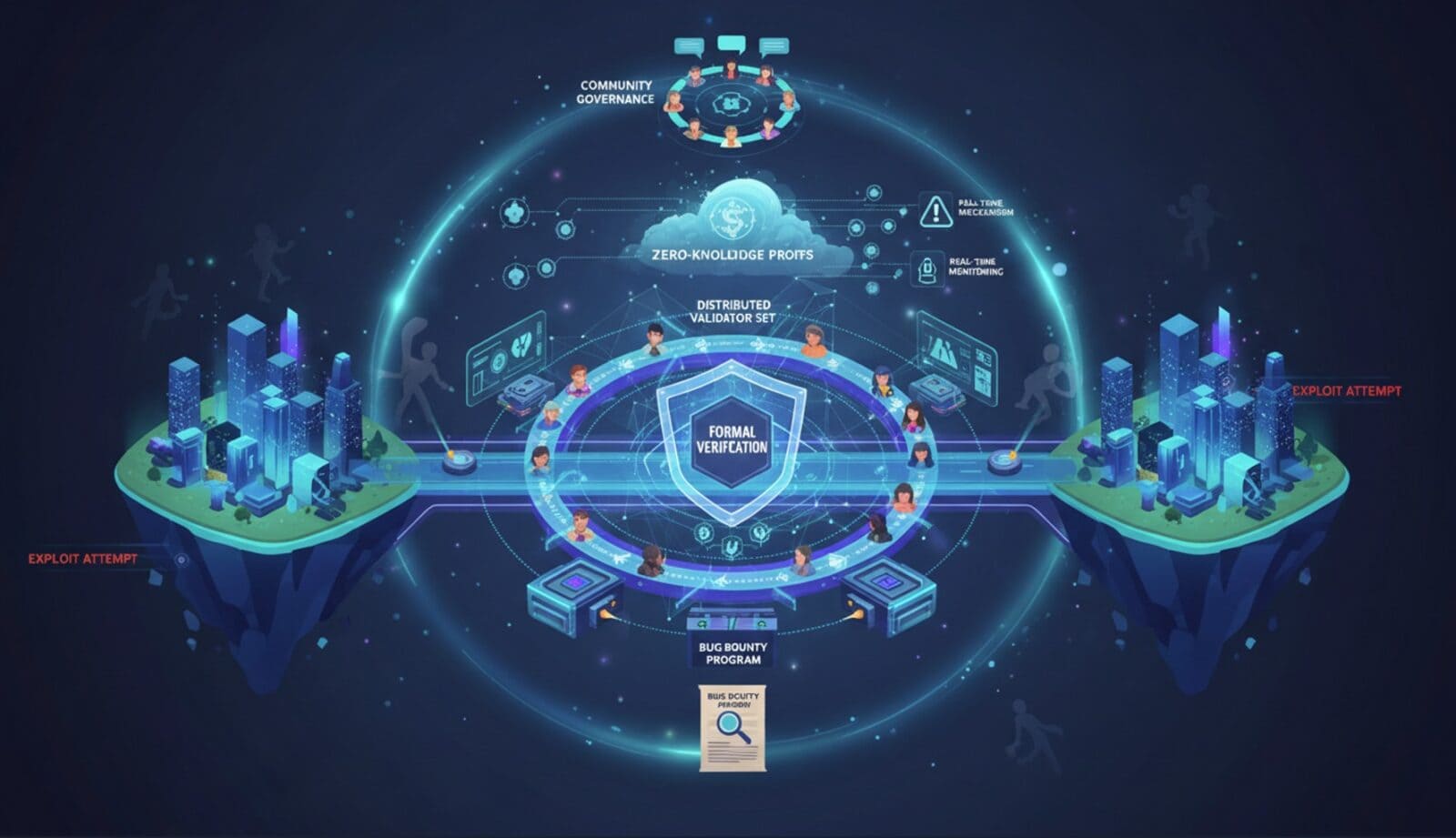
- Distributed Management: Utilizing distributed sets of validators and implementing strict operational security to manage private keys more securely.
- Active Monitoring and Emergency Protocols: Deploying systems that can detect suspicious activity instantly and respond by halting operations can mitigate the impact of breaches.
- Preventive Controls: Establishing rate limits and withdrawal caps can limit the damage even after a security breach occurs.
- Continuous Improvement: Regular security audits, bug bounty programs, and ongoing vulnerability assessments are crucial in adapting to new threats over time.
The Future Roadmap for Bridge Security
As blockchain continues to evolve towards a multi-chain future, the development of more secure, robust bridge structures is critical. Innovations such as decentralized validation and advanced cryptographic proofs are on the rise, aiming to diminish reliance on trust and enhance security frameworks. These efforts, along with improved standards and tools, are crucial for building resilient bridges that can support the expansive growth of decentralized networks.
Final Thoughts
Blockchain bridges are indispensable for the advancement of Web3, enabling expansive multi-chain interactions. However, the complexities and high-value assets they deal with make them particularly vulnerable to attack. To foster continued growth and gain trust, the industry must prioritize comprehensive, forward-thinking security measures that ensure both robustness and resilience against evolving threats.


















STAY ALWAYS UP TO DATE